Evaluating Computer Architectures and the Impact on Next Generation Computing: New Approach to Solving Computationally Difficult, Data-Intensive Problems
Create and release your Profile on Zintellect – Postdoctoral applicants must create an account and complete a profile in the on-line application system. Please note: your resume/CV may not exceed 2 pages.
Complete your application – Enter the rest of the information required for the IC Postdoc Program Research Opportunity. The application itself contains detailed instructions for each one of these components: availability, citizenship, transcripts, dissertation abstract, publication and presentation plan, and information about your Research Advisor co-applicant.
Additional information about the IC Postdoctoral Research Fellowship Program is available on the program website located at: https://orise.orau.gov/icpostdoc/index.html.
If you have questions, send an email to ICPostdoc@orau.org. Please include the reference code for this opportunity in your email.
Research Topic Description, including Problem Statement:
Increasingly, the Intelligence Community (IC) is required to solve more computationally difficult, data-intensive problems (e.g., cyber defense) that can have an impact on national security objectives. Consequently, the underlying principles that define the relationships between computer architectures and Big Data applications must be better understood in order for the IC to achieve its desired outcomes. Conversely, the ability of computer structures to meet Big Data application requirements effectively, reliably, and within prevailing technological constraints must also be better understood. In particular, some data-intensive applications require computational capabilities that demand heavy numerical calculations. In recent years, artificial intelligence/machine learning (AI/ML) has emerged as an important tool for improving the performance of conventional systems and for developing novel methods for tackling computationally difficult problems. An important requirement is to maximize algorithm performance by minimizing CPU and I/O inefficiencies for computationally intensive tasks. Currently, industry standard methods are: insufficient, do not scale, and frequently result in missing or dropped data that can significantly impact critical decisions.
Example Approaches:
Develop and deploy novel capabilities that can enable applications critical to the IC (e.g., cyber defense) to be more quickly and efficiently addressed; Examine larger pipelines with higher data volumes and velocities to better meet requirements; Improve performance of cybersecurity workflows; Examine zero trust architecture and ability of ML to deliver solutions that can enhance the security posture of computer networks.
Relevance to the Intelligence Community (IC):
Problems to be Considered:
- Traditional methods and tools are not fast enough and rely too heavily on heuristics.
- Log collection outpaces Analysis—the amount and quantity of logs collected on, and devices added to network continues to increase.
- Managing large-scale, heterogeneous deployments for cybersecurity is challenging.
- More complex models give additional inference capabilities, but they are difficult to scale and deploy in real-time environments.
Key Words: #Data-Intensive Applications, #Artificial Intelligence, #Machine Learning, #Algorithm, #Big Data, #Computer Architectures, #CPU, #I/O, #Cyber Defense
Postdoc Eligibility
- U.S. citizens only
- Ph.D. in a relevant field must be completed before beginning the appointment and within five years of the application deadline
- Proposal must be associated with an accredited U.S. university, college, or U.S. government laboratory
- Eligible candidates may only receive one award from the IC Postdoctoral Research Fellowship Program
Research Advisor Eligibility
- Must be an employee of an accredited U.S. university, college or U.S. government laboratory
- Are not required to be U.S. citizens
- Citizenship: U.S. Citizen Only
- Degree: Doctoral Degree.
-
Discipline(s):
- Chemistry and Materials Sciences (12 )
- Communications and Graphics Design (4 )
- Computer, Information, and Data Sciences (17 )
- Earth and Geosciences (21 )
- Engineering (27 )
- Environmental and Marine Sciences (14 )
- Life Health and Medical Sciences (48 )
- Mathematics and Statistics (11 )
- Other Non-Science & Engineering (2 )
- Physics (16 )
- Science & Engineering-related (1 )
- Social and Behavioral Sciences (29 )

 ORISE GO
ORISE GO
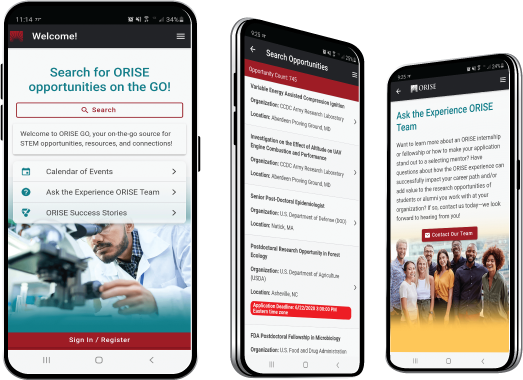
The ORISE GO mobile app helps you stay engaged, connected and informed during your ORISE experience – from application, to offer, through your appointment and even as an ORISE alum!





