Create and release your Profile on Zintellect – Postdoctoral applicants must create an account and complete a profile in the on-line application system. Please note: your resume/CV may not exceed 2 pages.
Complete your application – Enter the rest of the information required for the IC Postdoc Program Research Opportunity. The application itself contains detailed instructions for each one of these components: availability, citizenship, transcripts, dissertation abstract, publication and presentation plan, and information about your Research Advisor co-applicant.
Even those who are not familiar with law enforcement or intelligence practices should, by now, have a basic understanding of biometrics from the popularity of television crime dramas, such as CSI. As the law enforcement and intelligence communities (as well as private industry) move towards using more biometrics to define a user or suspect, the challenge remains that no single biometric method is likely to ever be completely accurate. Not only does this reduce confidence in the accuracy of any given biometric result, but it also limits the ability of the user to adequately triage large volumes of data based on a single biometric modality.
This is where multimodal biometrics comes in. Multimodal biometrics involves the use of multiple characteristics, used in conjunction, to identify an individual. Different biometric technologies utilize a variety of characteristics to identify subjects, including facial appearance (i.e., facial recognition), fingerprints, iris, voice, handwriting, gait, scent, and ear features. All of these, on their own, are subject to limitations. What is of most significance to the intelligence community, however, is that the accuracy of any single given biometric technology may not be adequate to identify a target with high confidence when the input signal is of low quality (e.g., CCTV images or voicemail recording from a call made on a cell phone). What the intelligence community needs is a better way to take advantage of lower quality biometric signatures.
Digital multimedia offers an opportunity to do that. For the law enforcement and intelligence communities, digital multimedia is becoming more common as material to be exploited and it often includes both visual and audio information. Within the law enforcement and intelligence communities there is an increasingly large amount of multimedia data which is often times examined forensically to identify individuals depicted in this data. This data may be recovered from suspects’ computers or from social media sites. Of particular interest, video recordings which depict people speaking (whether directly to the camera or not) are becoming more and more the subject of these forensic examinations. This offers the potential for a multimodal biometric approach utilizing facial recognition and speaker recognition.
Although current algorithms for both face recognition and speaker recognition are relatively robust under highly controlled circumstances, their performance degrades with lower quality data – including the type of data under consideration here. While improvement of algorithms in each modality is likely to be a continuing area of research, a new line of investigation is proposed to actively consider how one can fuse existing face and speaker recognition solutions to generate higher matching confidence.
Therefore, the community at large is seeking a solution to strengthen the ability to create a match using a fusion of face recognition and speaker recognition technologies. Such solutions are not only needed to strengthen the results of one exam, but also to perform automated recognition across large volumes of data (i.e., “Big Data”).
Example Approaches
Proposals should consider the fusion of a variety of biometric modalities. Research could consider, but not be limited to, the examples below:
Automated facial recognition and speaker recognition approaches are quite mature at this time. Current commercial implementations of automatic facial recognition are derived from two major approaches: geometric (feature based) and photometric (view based). The latter approach has become quite robust to slight changes in pose, angle, illumination and expression, making practical application of facial recognition a reality in many operational scenarios.
In general, speaker recognition system used in forensic or investigative application is composed of acquisition and preprocessing of voice samples, feature extractor that generates feature vectors, and the classifier (or matching) engine which generates matching scores. Trained human analysts interpret matching scores for match, no match, or inconclusive as their final conclusions. Today’s main stream advanced speaker recognition system uses MFCCs_based i-Vector and PLDA classifier to generate matching scores in the form of Likelihood Ratio (LR) or Log Likelihood Ratio (LLR) scores, normalized or non-normalized, and calibrated or non-calibrated.
The fact that face and voice features can be safely assumed to be independent from each other, and the fact that scores from speaker recognition system are generative, and based on the probabilities, voice makes an ideal choice of a biometric modality to be fused with output of the facial recognition system. There are various stages in the recognition process where fusion can take place in voice and face recognition systems, the simplest and the most effective stage appears to be after the matching scores are generated. The ultimate multimodal biometric system we are seeking will be one which ingests scores (LLRs, etc.) from both face and voice recognition systems, fuse the two scores into a single score, normalize it, and calibrate it as a final a score.

 ORISE GO
ORISE GO
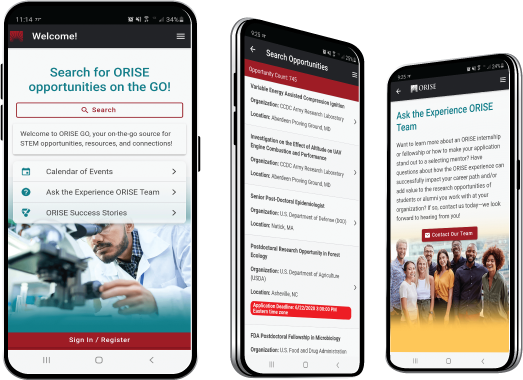
The ORISE GO mobile app helps you stay engaged, connected and informed during your ORISE experience – from application, to offer, through your appointment and even as an ORISE alum!
You gave a rating of 0 star(s)
SECURITY/PRIVACY NOTICE
By continuing to use this system you indicate your awareness of and consent to the following terms and conditions of use. LOGOUT IMMEDIATELY if you do not agree to the conditions stated in this warning.
SECURITY NOTICE
This system is part of a Federal information system. This system is monitored for security purposes to ensure it remains available to all users and to protect information in the system. The system employs software programs to monitor network traffic to identify unauthorized activities. By accessing this system, you are expressly consenting to these monitoring activities. Unauthorized attempts to defeat or circumvent security features; to use the system for other than intended purposes; to deny service to authorized users; to access, obtain, alter, damage, or destroy information; to upload or change information; to otherwise cause system or information damage; or otherwise to interfere with the system or its operation, is prohibited. Evidence of such acts may be dis-closed to law enforcement authorities and result in prosecution under the Computer Fraud and Abuse Act of 1986 and the National Information Infrastructure Protection Act of 1996, or other applicable laws.
PRIVACY NOTICE
This system is for authorized use only. Use of this system constitutes consent to security monitoring and testing. All activity is logged with your host name and IP address. Users (authorized or unauthorized) have no explicit or implicit expectation of privacy. Any or all uses of this system and all files on this system may be intercepted, monitored, recorded, copied, audited, inspected, and dis-closed to authorized site and law enforcement personnel, as well as authorized officials of other agencies, both domestic and foreign. By using this system, the user consents to such interception, monitoring, recording, copying, auditing, inspection, and disclosure at the discretion of authorized site or law enforcement personnel. Unauthorized or improper use of this system may result in administrative disciplinary action and civil and criminal penalties.
You have been inactive on this page for . You will be logged out after 03:00:00.
Select an icon below to visit the website and download an appropriate browser.
For help, please email Zintellect@orau.org.
Question: What is the deadline for submitting an application?
Answer: Not all opportunities have application deadlines. Some opportunities remain open until they are filled. If an opportunity has an application deadline, then it will be listed in the opportunity details or in the opportunity catalog.
Question: How do I reset my password?
Answer: If you have forgotten your password or wish to reset your password, use the "Forgot password or username?" tab on the login to reset it.
Question: I forgot my username. How do I retrieve it?
Answer: Use the "Forgot password or username?" tab on the login. You will receive an email containing your username.
Question: What do I need to submit an application?
Answer: Typically, applicants are required to submit a resume or CV, an official copy of their transcripts or academic record, and a minimum of two references at the time they apply. Additional requirements such as a writing sample, thesis or dissertation, etc. may be required. Review the opportunity details for additional information about the requirements for applying for an opportunity.
Question: Where do I upload my transcripts?
Answer: If required, you will be asked to upload your transcript as a part of the application process.
Question: Where do I submit a writing sample?
Answer: If required, you will be asked to upload a writing sample as part of the application process.
Question: Can a family member serve as a reference?
Answer: No; family members may not serve as references. References must be able to speak to your educational and/or professional experience. At least one academic reference is preferred.
Our Zintellect A.I. is constantly learning how to Match you to our opportunities! So, we want to know when we get it right or when we get it wrong. This will help us make our better! Plus, as a potential applicant to one of our many opportunities across the country, we value you and want to help you on your career path!