Automated Crypto Asset Transfer Provenance Reconstruction Fellowship
Create and release your Profile on Zintellect – Postdoctoral applicants must create an account and complete a profile in the on-line application system. Please note: your resume/CV may not exceed 3 pages.
Complete your application – Enter the rest of the information required for the IC Postdoc Program Research Opportunity. The application itself contains detailed instructions for each one of these components: availability, citizenship, transcripts, dissertation abstract, publication and presentation plan, and information about your Research Advisor co-applicant.
Additional information about the IC Postdoctoral Research Fellowship Program is available on the program website located at: https://orise.orau.gov/icpostdoc/index.html.
If you have questions, send an email to ICPostdoc@orau.org. Please include the reference code for this opportunity in your email.
Research Topic Description, including Problem Statement:
Digital or technology-related financial frauds and crypto-asset based crime are rapidly increasing, threatening the Australian community’s financial security, national economic stability and our national security. With the advent of cryptocurrencies, digital assets, distributed ledger technologies and services, and digital payments, identifying the perpetrators and enablers of these crimes has become more difficult.
While identification of useful data (to tackle crime-related fraudulent transactions) within big data sources is a well-known challenge, the ability to interrogate big data sources that have only recently been established outside traditional banking systems presents additional challenges. The ability to detect and disrupt suspicious transactions by crime syndicates in real time within these new platforms, and those soon to emerge, is the challenge.
Complex and non-standardized data structure of numerous digital payment systems limit the ease of access to and query-ability of raw data across multiple networks. Crypto-asset systems don’t share the same data formats (heterogeneous) and block header fields. Obfuscation and anonymization techniques serve to hide communication and transfer routes, by design. These features make legal establishment of provenance much harder. Real-time multi-source data sets need suitable mechanisms to identify and extract effective features and integrate heterogenous data efficiently.
Example Approaches:
This proposal aims to adopt the following approaches:
- Efficiently integrate multi-source heterogeneous data from open source for real time analysis.
- Advanced data analytics algorithms capable to handle streaming big data in real time.
- Unsupervised machine learning algorithms capable to classify unlabeled multidimensional data to facilitate detection of suspicious transactions.
The big data analytics algorithms developed during this project would exploit the hidden connections and reveal the linkages to automatically reconstruct the provenance, i.e. information flows and payment histories of suspicious activities in almost real-time. Specifically, the project aims to develop novel data mining techniques where the algorithms can handle variable dimensional transaction data and massive amounts of streaming data having a small number of points of interest (fraudulent transactions) to correlate and detect suspicious crypto asset transactions in real time.
Relevance to the Intelligence Community:
The outcome of this project may benefit the challenges in anti-money laundering and counter terrorism financing mainly with the two aspects by providing:
- Data Aggregator - a novel blockchain protocol ensembler enabling access to heterogeneous data streams. These include data captured using open-source APIs such as bitcoinexplorer.org, etherscan.io, coinatmradar.com etc.
- Vector Similarity Search Module - based on graph neural network (GNN) model using Faiss, pinecone, milvus etc. to identify inter-cohort interaction.
References:
- Definitions of Vector Databases: https://learn.microsoft.com/en-us/semantic-kernel/memories/vector-db.
- Features of a Vector Database: https://mlops.community/empowering-language-model-applications-understanding-and-evaluating-vector-databases-in-production/.
- Vector Databases vs Vector L braries: https://lakefs.io/blog/12-vector-databases-2023/.
- Types of Databases: https://www.datacamp.com/blog/the-top-5-vector-databases.
- Vector database table: https://objectbox.io/vector-database/.
- Embedding creation: https://mlops.community/vector-similarity-search-from-basics-to-production/.
- Pros & Cons: https://www.linkedin.com/pulse/unleashing-power-vectors-embeddings-vector-databases-huaping-gu/.
Key Words: Digital payments, Crypto asset transfer, Provenance reconstruction.
Postdoc Eligibility
- U.S. citizens only
- Ph.D. in a relevant field must be completed before beginning the appointment and within five years of the appointment start date
- Proposal must be associated with an accredited U.S. university, college, or U.S. government laboratory
- Eligible candidates may only receive one award from the IC Postdoctoral Research Fellowship Program
Research Advisor Eligibility
- Must be an employee of an accredited U.S. university, college or U.S. government laboratory
- Are not required to be U.S. citizens
- Citizenship: U.S. Citizen Only
- Degree: Doctoral Degree.
-
Discipline(s):
- Chemistry and Materials Sciences (12 )
- Communications and Graphics Design (6 )
- Computer, Information, and Data Sciences (17 )
- Earth and Geosciences (21 )
- Engineering (27 )
- Environmental and Marine Sciences (14 )
- Life Health and Medical Sciences (45 )
- Mathematics and Statistics (10 )
- Other Non-Science & Engineering (2 )
- Physics (16 )
- Science & Engineering-related (1 )
- Social and Behavioral Sciences (30 )

 ORISE GO
ORISE GO
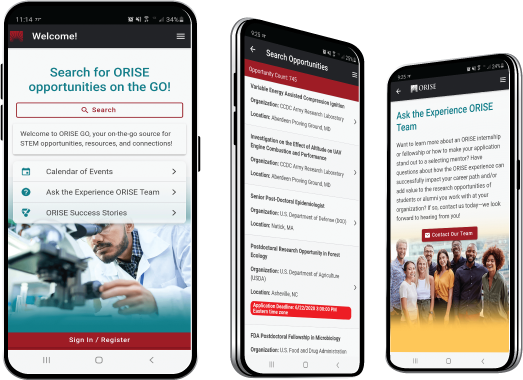
The ORISE GO mobile app helps you stay engaged, connected and informed during your ORISE experience – from application, to offer, through your appointment and even as an ORISE alum!





