Finding Agency in Sensory Data
Create and release your Profile on Zintellect – Postdoctoral applicants must create an account and complete a profile in the on-line application system. Please note: your resume/CV may not exceed 2 pages.
Complete your application – Enter the rest of the information required for the IC Postdoc Program Research Opportunity. The application itself contains detailed instructions for each one of these components: availability, citizenship, transcripts, dissertation abstract, publication and presentation plan, and information about your Research Advisor co-applicant.
Additional information about the IC Postdoctoral Research Fellowship Program is available on the program website located at: https://orise.orau.gov/icpostdoc/index.html.
If you have questions, send an email to ICPostdoc@orau.org. Please include the reference code for this opportunity in your email.
Research Topic Description, including Problem Statement:
The present-day era of cybersecurity is largely defined by defense from hostile code interventions (such as ransomware and viruses) and hostile intrusion through weak access controls. We believe that many present-day cyber-physical systems will evolve towards large scale, highly interdependent, collectives of agents having emergent properties. We therefore expect future cybersecurity challenges to evolve to include defense from malicious agency.
We believe that emergence is a consequence of interaction/interdependency between agents (cyber-physical components), and that the properties, although absent in the individuals, exists in the collective. These are complex systems. The nature of emergence drives us towards the use of models of agency for the cybersecurity of collectives because of the symmetrical relationship between attacker and defender – we assert that future cyber conflict will partly lie in the emergent space of complex systems. Complex systems are nonlinear, emergent, with diverse internal components, use feedback mechanisms, are autonomous in behavior, adaptive, and capable of learning. They use intensive internal communications to balance system cohesion with the forces of adaptability, and to work as a collective towards a common goal. They are unstable and may alternate unpredictably between seemingly random and stable patterns of behavior. This makes complex cyber-physical systems vulnerable to cyberattack in new ways, but we think the emergent properties are also a potential asset in responding to this threat - malicious agency could be countered by benevolent agency.
Example Approaches:
Biology provides the following inspiration:
- Life-as-a-system inspires the engineering of technological systems – life has emergent properties and is increasingly being understood in terms of systems theory
- Classification of life systems (cladistics) inspires the characterization of agency as traits (apomorphies) – this may be transferrable to machine learning applied to sensory data sets
- Life systems demonstrate complexity, and therefore provide worked examples suitable for informing engineering
Possible approaches:
- Analysis of non-parsimonious decision trees using phylogenetic tree analysis techniques from evolutionary biology (cladistics) – does the digital shadow left by agency in sensory data correspond meaningfully to apomorphies and/or synapomorphies?
- Modelling the behavior of cyber-physical systems as simple cybernetic regulatory systems – using systems theory to determine irregular behavior indicative of malicious agency. Examples from nature are given by Camazine & Deneubourg (2003) [2]
- Modelling the behavior of complex adaptive systems – perhaps with the “Revealed Dynamics Markov Model” (Bramson, 2019 [1] pp79-128)
Principal challenges:
- The appropriateness of techniques from evolutionary biology – determining when there is sufficient lack of parsimony for the required degrees of freedom and, when so, to extract meaningful characterizations of behavior (apomorphies) from noisy data using techniques from biology
- Characterizing behavior and agency in systems – creating agent-based models that are similar to malicious agency so that detection in sensory data from the digital shadow can be demonstrated.
- Comparing evidence from digital shadows with putative behavior models – bridging the gap between a sensory representation and a behavioral one. We also need to decide when a correspondence between a hypothesized agency and our model of that agency has occurred.
- Defining maliciousness – At some point, we will need to define what we mean by a “malicious agency”. Karnouskos (2015) [3] discusses this in terms of the exploitation of one agent by another (this could be seen as the perversion or obstruction of the victim agent’s mission goal by an attacking agent).
Refs:
[1] Ted Carmichael (Editor), Andrew J. Collins (Editor), Mirsad Hadžikadic (Editor), Complex Adaptive Systems: Views from the Physical, Natural, and Social Sciences (Understanding Complex Systems), Springer; 1st ed. 2019 edition (27 Jun. 2019), ISBN-13: 978-3030203078
[2] Scott Camazine (Author), Jean-Louis Deneubourg (Author), Nigel R. Franks (Author), Self-Organization in Biological Systems: 38 (Princeton Studies in Complexity), Princeton University Press (17 Sept. 2003), ISBN-13: 978-0691116242
[3] Stamatis Karnouskos, Chapter 6 - Industrial Agents Cybersecurity, Editor(s): Paulo Leitão, Stamatis Karnouskos, Industrial Agents, Morgan Kaufmann, 2015, Pages 109-120, ISBN 9780128003411, https://doi.org/10.1016/B978-0-12-800341-1.00006-1. (https://www.sciencedirect.com/science/article/pii/B9780128003411000061)
Postdoc Eligibility
- U.S. citizens only
- Ph.D. in a relevant field must be completed before beginning the appointment and within five years of the application deadline
- Proposal must be associated with an accredited U.S. university, college, or U.S. government laboratory
- Eligible candidates may only receive one award from the IC Postdoctoral Research Fellowship Program
Research Advisor Eligibility
- Must be an employee of an accredited U.S. university, college or U.S. government laboratory
- Are not required to be U.S. citizens
Key Words: Cybersecurity, Cyber Systems, Emergence, Complex Systems
- Citizenship: U.S. Citizen Only
- Degree: Doctoral Degree.
-
Discipline(s):
- Chemistry and Materials Sciences (12 )
- Communications and Graphics Design (6 )
- Computer, Information, and Data Sciences (17 )
- Earth and Geosciences (21 )
- Engineering (27 )
- Environmental and Marine Sciences (14 )
- Life Health and Medical Sciences (48 )
- Mathematics and Statistics (11 )
- Other Non-Science & Engineering (2 )
- Physics (16 )
- Science & Engineering-related (1 )
- Social and Behavioral Sciences (29 )

 ORISE GO
ORISE GO
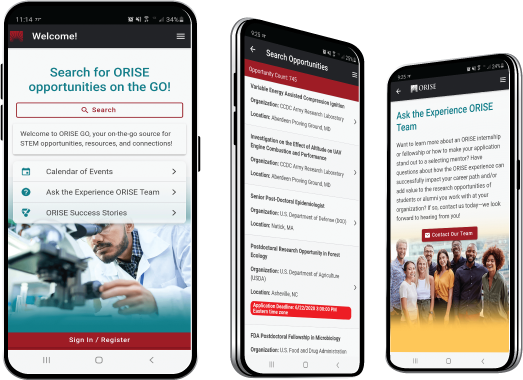
The ORISE GO mobile app helps you stay engaged, connected and informed during your ORISE experience – from application, to offer, through your appointment and even as an ORISE alum!





