Protect Individuals and Our Workspaces from Acoustic Compromise, Through the Identification of Threats and Countermeasures
Create and release your Profile on Zintellect – Postdoctoral applicants must create an account and complete a profile in the on-line application system. Please note: your resume/CV may not exceed 2 pages.
Complete your application – Enter the rest of the information required for the IC Postdoc Program Research Opportunity. The application itself contains detailed instructions for each one of these components: availability, citizenship, transcripts, dissertation abstract, publication and presentation plan, and information about your Research Advisor co-applicant.
Additional information about the IC Postdoctoral Research Fellowship Program is available on the program website located at: https://orise.orau.gov/icpostdoc/index.html.
If you have questions, send an email to ICPostdoc@orau.org. Please include the reference code for this opportunity in your email.
Research Topic Description, including Problem Statement:
There are three areas of acoustic compromise that we wish to explore. The first is related to speech, the second is related to the field of infrasound disruption, and the third is related to ultrasound egress.
With regards to speech, there are three key elements of interest. The first is to assure privacy of speech between individuals. The second is ensuring speech can be safely contained in a given space. The third is ensuring that you can protect an eavesdropping attack through egress of audio on other carriers. Each of these elements are important for the individual, the information content, and the organization in which they work.
With regards to infrasound, developing detection and countermeasures to radiated harmful effects. For ultrasound, certain levels can also be harmful to occupants, but they can also provide intelligence egress utilizing third party methods such as mobile phone signals or other methods etc.
We would like to explore the science of acoustics and if there are any opportunities or insights that can identify threats, provide closer attention for future work; or immediate opportunities to develop bespoke counter measures to protect UK assets.
In addition, we would like to understand and protect remote workers; offer best practice for protection of speech and any innovation that we could develop further. For example, particular interest is to examine the acoustic integrity of headsets that are routinely worn both at home and in office environments, which have now become commonplace during the pandemic during online meetings. Another measure is to examine how spaces could be better protected to ensure that speech is safely contained in an area (MSVE), either a designated purpose-built environment; a rapid deployment of a structure; or other practical countermeasures. Similarly, protection from ultrasound and infrasound.
The identification of particular security problems and proposed countermeasures is of primary interest for both individuals and workspaces.
An ideal deliverable would be the ability to acoustically model ‘a design’ of environments with differing materials, prior to construction. The model would determine and guide material or design choices to achieve attenuation necessary to provide a MSVE requirement at an early stage.
Metamaterials as an emerging technology in production methodology, could these be engineered to offer retrospective installation into a building fabric for a cost-effective audio suppression or directional control over acoustical waves?
We appreciate that this is a broad topic covering many aspects of acoustic research, therefore, we would welcome any expressions of interest in all or part of the above.
Example Approaches:
- Commercial company (USA) Holosonics produce directional speakers that could have a security use.
- Government sponsors have used disruptive technologies in the acoustic ranges, specifically sub aural, potential news articles report these being used, plus examples of use in crowd control. Directional speakers.
Glossary:
*MSVE – Minimum Safe Vocal Effort. A level of speech (dB) in an environment that cannot be overheard (by third parties).
Postdoc Eligibility
- U.S. citizens only
- Ph.D. in a relevant field must be completed before beginning the appointment and within five years of the application deadline
- Proposal must be associated with an accredited U.S. university, college, or U.S. government laboratory
- Eligible candidates may only receive one award from the IC Postdoctoral Research Fellowship Program
Research Advisor Eligibility
- Must be an employee of an accredited U.S. university, college or U.S. government laboratory
- Are not required to be U.S. citizens
Key Words: Acoustics, Ultrasound, Infrasound, Directional Speakers, Acoustic Disruption, ‘MSVE’, Metamaterials
- Citizenship: U.S. Citizen Only
- Degree: Doctoral Degree.
-
Discipline(s):
- Chemistry and Materials Sciences (12 )
- Communications and Graphics Design (6 )
- Computer, Information, and Data Sciences (17 )
- Earth and Geosciences (21 )
- Engineering (27 )
- Environmental and Marine Sciences (14 )
- Life Health and Medical Sciences (48 )
- Mathematics and Statistics (11 )
- Other Non-Science & Engineering (2 )
- Physics (16 )
- Science & Engineering-related (1 )
- Social and Behavioral Sciences (29 )

 ORISE GO
ORISE GO
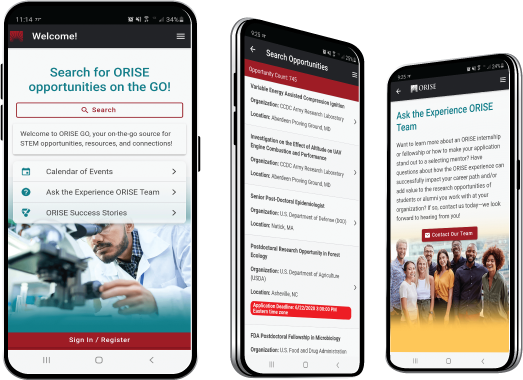
The ORISE GO mobile app helps you stay engaged, connected and informed during your ORISE experience – from application, to offer, through your appointment and even as an ORISE alum!





