Create and release your Profile on Zintellect – Postdoctoral applicants must create an account and complete a profile in the on-line application system. Please note: your resume/CV may not exceed 2 pages.
Complete your application – Enter the rest of the information required for the IC Postdoc Program Research Opportunity. The application itself contains detailed instructions for each one of these components: availability, citizenship, transcripts, dissertation abstract, publication and presentation plan, and information about your Research Advisor co-applicant.
Additional information about the IC Postdoctoral Research Fellowship Program is available on the program website located at: https://orise.orau.gov/icpostdoc/index.html.
If you have questions, send an email to ICPostdoc@orau.org. Please include the reference code for this opportunity in your email.
Research Topic Description, including Problem Statement:
There is a vast amount of literature around imbalanced learning. Solving imbalanced learning problems is critical in numerous data-intensive networked systems, including surveillance, security, cyber, finance, biomedical, defense, and more. Some recommendations to tackle the class-imbalance problem are collecting more labeled data, changing performance metric, resampling of data, generating synthetic samples, trying various classification algorithms and penalizing the models for mistakes on minority classes. Almost all of these solutions utilize an element of randomization, which leads to different detection outcomes from a single classification algorithm. This research aims at embedding supervised learning practice in preprocessing to build a deterministic data resampling for the benefit of underlying anomaly detection methods. It is like building a stack of hay-aware needles alongside the existing haystack to increase the chance of picking the lost needle.
Example Approaches:
Undersampling mainly involves random selection of majority samples to balance them with the minority ones. In contrast, oversampling mostly generates random samples considering the statistics in minority samples to balance them with the majority ones. This research intends to employ majority statistics and minority guidelines to train a novel supervised resampling model ahead of conventional classification or anomaly detection phase in the pipeline. The core idea is that generating augmented minority samples should minimize inter-class variance while maximizing intra-class discrepancy (Fisher Discrimination). Synthetic samples should likely mimic both minority and majority patterns to build a high-quality deterministic class-balanced data fed to the classification/detection phase.
Relevance to the Intelligence Community:
Intelligence agencies frequently deal with ‘incomplete’ datasets with few identified targets. Efforts to resolve the imbalanced learning problem may help agencies improve the accuracy of their analytic approaches to identify ‘unknown known’ targets within collected datasets despite the challenges of incomplete data. Real-world intelligence practice deals with few hostile anomalies compared to the large number of legitimate actions. Detection of these anomalies is of critical due to the possible damage that they can impose to the national interests and community well-beings. Due to infinitesimal ratio of anomalies to normal behaviors, i.e. passengers importing illicit goods vs all other travellers, machine learning techniques usually suffer from class-imbalance syndrome and cannot produce viable detections. This research will address this shortcoming by applying supervised learning to build context-aware class-balanced training data for maximizing detection performance to find needles in a haystack.
Key Words: Machine Learning, Supervised Learning, Imbalanced Data, Anomaly Detection, Oversampling, Undersampling

 ORISE GO
ORISE GO
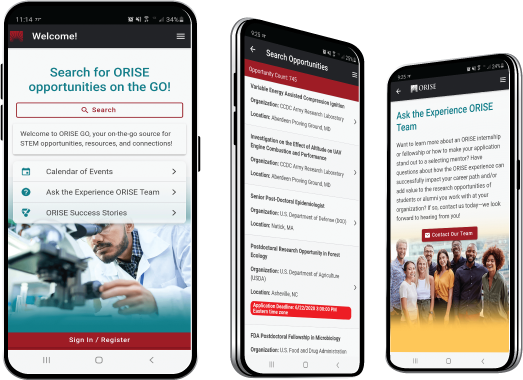
The ORISE GO mobile app helps you stay engaged, connected and informed during your ORISE experience – from application, to offer, through your appointment and even as an ORISE alum!
You gave a rating of 0 star(s)
SECURITY/PRIVACY NOTICE
By continuing to use this system you indicate your awareness of and consent to the following terms and conditions of use. LOGOUT IMMEDIATELY if you do not agree to the conditions stated in this warning.
SECURITY NOTICE
This system is part of a Federal information system. This system is monitored for security purposes to ensure it remains available to all users and to protect information in the system. The system employs software programs to monitor network traffic to identify unauthorized activities. By accessing this system, you are expressly consenting to these monitoring activities. Unauthorized attempts to defeat or circumvent security features; to use the system for other than intended purposes; to deny service to authorized users; to access, obtain, alter, damage, or destroy information; to upload or change information; to otherwise cause system or information damage; or otherwise to interfere with the system or its operation, is prohibited. Evidence of such acts may be dis-closed to law enforcement authorities and result in prosecution under the Computer Fraud and Abuse Act of 1986 and the National Information Infrastructure Protection Act of 1996, or other applicable laws.
PRIVACY NOTICE
This system is for authorized use only. Use of this system constitutes consent to security monitoring and testing. All activity is logged with your host name and IP address. Users (authorized or unauthorized) have no explicit or implicit expectation of privacy. Any or all uses of this system and all files on this system may be intercepted, monitored, recorded, copied, audited, inspected, and dis-closed to authorized site and law enforcement personnel, as well as authorized officials of other agencies, both domestic and foreign. By using this system, the user consents to such interception, monitoring, recording, copying, auditing, inspection, and disclosure at the discretion of authorized site or law enforcement personnel. Unauthorized or improper use of this system may result in administrative disciplinary action and civil and criminal penalties.
You have been inactive on this page for . You will be logged out after 03:00:00.
Select an icon below to visit the website and download an appropriate browser.
For help, please email Zintellect@orau.org.
Question: What is the deadline for submitting an application?
Answer: Not all opportunities have application deadlines. Some opportunities remain open until they are filled. If an opportunity has an application deadline, then it will be listed in the opportunity details or in the opportunity catalog.
Question: How do I reset my password?
Answer: If you have forgotten your password or wish to reset your password, use the "Forgot password or username?" tab on the login to reset it.
Question: I forgot my username. How do I retrieve it?
Answer: Use the "Forgot password or username?" tab on the login. You will receive an email containing your username.
Question: What do I need to submit an application?
Answer: Typically, applicants are required to submit a resume or CV, an official copy of their transcripts or academic record, and a minimum of two references at the time they apply. Additional requirements such as a writing sample, thesis or dissertation, etc. may be required. Review the opportunity details for additional information about the requirements for applying for an opportunity.
Question: Where do I upload my transcripts?
Answer: If required, you will be asked to upload your transcript as a part of the application process.
Question: Where do I submit a writing sample?
Answer: If required, you will be asked to upload a writing sample as part of the application process.
Question: Can a family member serve as a reference?
Answer: No; family members may not serve as references. References must be able to speak to your educational and/or professional experience. At least one academic reference is preferred.
Our Zintellect A.I. is constantly learning how to Match you to our opportunities! So, we want to know when we get it right or when we get it wrong. This will help us make our better! Plus, as a potential applicant to one of our many opportunities across the country, we value you and want to help you on your career path!