Robust Physical Layer Security for Wireless Communications
Create and release your Profile on Zintellect – Postdoctoral applicants must create an account and complete a profile in the on-line application system. Please note: your resume/CV may not exceed 2 pages.
Complete your application – Enter the rest of the information required for the IC Postdoc Program Research Opportunity. The application itself contains detailed instructions for each one of these components: availability, citizenship, transcripts, dissertation abstract, publication and presentation plan, and information about your Research Advisor co-applicant.
Additional information about the IC Postdoctoral Research Fellowship Program is available on the program website located at: https://orise.orau.gov/icpostdoc/index.html.
If you have questions, send an email to ICPostdoc@orau.org. Please include the reference code for this opportunity in your email.
Research Topic Description, including Problem Statement:
Current networks need to send large amounts of data efficiently and securely between multiple different points. Many methods for implementing physical layer security are inefficient, have difficulty in the presence of multipath and fading channels and/or lack the ability to be implemented for multiple users having simultaneous access.
The goal of this topic is to explore and characterize the performance of physical layer security techniques especially in the presence of multipath and fading channels. The preference is for techniques that primarily utilize physics based approaches to improve security while keeping the links backwards compatible; however, novel approaches that utilize some communications information will be considered. The goal is to design an efficient modern communications system that can incorporate physical security techniques to increase the cost to eavesdroppers to intercept the signal. Characterizing any novel physical layer security needs to address this problem and will involve evaluating system efficiency as well as probability of detection and probability of interception both with and without a priori knowledge.
For any physical layer security technique, practical implementation should be considered including the impact of antenna element choice, array design, protocols, and data rates on error rates, mutual information and multi-user support. The report should also address the tradeoffs for power and system complexity versus the secrecy achieved by the link.
Example Approaches:
Security-oriented beamforming; artificial noise injection; directional modulation; orbital angular momentum (generates the illusion of higher order rotation in the EM field by superimposing phased contributions from an array of antenna elements) Secure Antenna Polarization Modulation (SAPM) (dual polarized antennas are used to create data distortion with an element of randomness at all transmission angles except the intended ones)
Relevance to the Intelligence Community:
- Increased security and privacy for a variety of communications networks
- Increased efficiency and reliability of networks using physical layer security techniques
Key Words: Wireless Communications, Physical Layer Security, Cybersecurity, Antenna Arrays
Postdoc Eligibility
- U.S. citizens only
- Ph.D. in a relevant field must be completed before beginning the appointment and within five years of the application deadline
- Proposal must be associated with an accredited U.S. university, college, or U.S. government laboratory
- Eligible candidates may only receive one award from the IC Postdoctoral Research Fellowship Program
Research Advisor Eligibility
- Must be an employee of an accredited U.S. university, college or U.S. government laboratory
- Are not required to be U.S. citizens
- Citizenship: U.S. Citizen Only
- Degree: Doctoral Degree.
-
Discipline(s):
- Chemistry and Materials Sciences (12 )
- Communications and Graphics Design (2 )
- Computer, Information, and Data Sciences (16 )
- Earth and Geosciences (21 )
- Engineering (27 )
- Environmental and Marine Sciences (14 )
- Life Health and Medical Sciences (45 )
- Mathematics and Statistics (10 )
- Other Non-Science & Engineering (2 )
- Physics (16 )
- Science & Engineering-related (1 )
- Social and Behavioral Sciences (27 )

 ORISE GO
ORISE GO
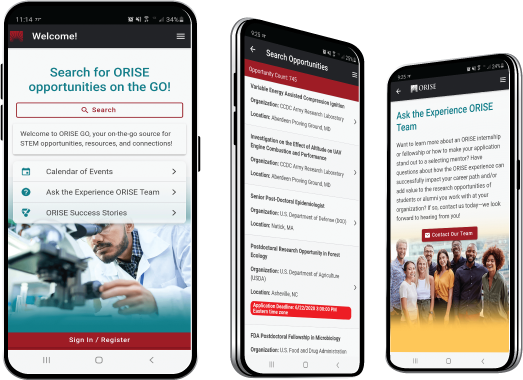
The ORISE GO mobile app helps you stay engaged, connected and informed during your ORISE experience – from application, to offer, through your appointment and even as an ORISE alum!





